System and Organization Controls 2 (SOC 2) is one of the key compliance requirements that technology-focused companies must meet today. The framework is set up to audit and evaluate policies and procedures for technology-based service organizations that store customer data and focuses on the following areas:
- Security
- Confidentiality
- Privacy of customer data
- Availability
- Processing integrity
Meeting SOC 2 compliance means establishing a consistent process and implementing solutions that guarantee oversight across the entire organization, especially when it comes to any unauthorized access or physical security of the facilities. In addition to establishing policies and procedures tracking and audit trails should be provided with detailed, uninterrupted information around who, what, when, where and how had access to facilities and technology inside an organization.
As part of SOC 2 compliance, organizations should also develop a proactive approach to preventing any incident that threatens the security, availability, confidentiality and privacy of customer data. Anyone visiting company sites can pose a potential threat, so the policies and procedures are required around the physical access to facilities.
For example, one of the controls (CC6.4)states:
“The entity restricts physical access to facilities and protected information assets (for XYZ, data center facilities, backup media storage, and other sensitive locations) to authorized personnel to meet the entity’s objectives.”
Protecting information assets and facility access controls are related to Visitor Management and are often solved by implementing a VMS (Visitor Management System) across organization’s sites.
Visitor management and SOC 2 controls
The early concept of a Visitor Management System (VMS) was a basic way to digitally sign-in guests more effectively. Now that Visitor Management has extended past the lobby, companies can capture data and have greater visibility of visitors throughout their building or multiple locations.
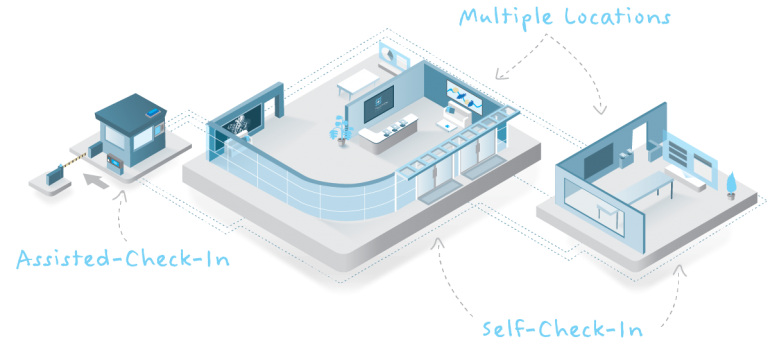
Adhering to the SOC 2 Type-2 standards means VMS provides an auditable, real-time tracking of guest data and mitigatesrisks introduced by having visitors (contractors, customers, potential customers, potential employees) at the facility.
Now, companies can have full sight on who enters and leaves their facilities. They have assurance that data collected from their VMS is private and only accessible by authorized officials. They have an accurate head count and ability to make real-time contact with every guest in case of an emergency or evacuation.
In the end, deploying a capable Visitor Management strategy is just as much about having confidence in your own daily safety and security measures as it is satisfying critical SOC 2 requirements.
“This requires a company to dedicate themselves to a standardized process in their global operation,” said Keith Metcalfe, CEO of Sign In Enterprise. “This requires consultation of many stakeholders in the line of business, facilities and security.”
“It allows for peace of mind,” said Metcalfe.
Sign In Enterprise’s SOC 2 certification
For many enterprise-level companies with critical infrastructure and technology to protect, having advanced security and compliance processes are top priorities. That standard also extends to the credibility and competency of their partners.
In the SaaS industry, achieving all of the levels of SOCcertification displays a serious commitment to customer data governance. In the fall of 2018, Sign In Enterprise reached a higher level, earning SOC 2 Type-1 attestation.
While that landmark serves as a solid foundation for protecting sensitive client data, we needed to go further in order to prove that we can consistently have these controls in place. Acquiring our SOC 2 Type-2 attestation would demonstrate to our customers that we highly value security, confidentiality and availability in our own operations.
Sign In Enterprise was audited from September 2018 to June 2019 by a third-party firm specializing in non-financial reporting controls. During the process, the firm assessed our controls, reporting and response efficacies. For companies with a cloud-based platform, the evaluating criteria is likely to be more strict.
Do we have processes to address a data breach? Can we adapt to changing technologies? Can we scale with our customer?
“Audits take time and money,” explained Caitlin Tuba, Data Protection Officer at Sign In Enterprise. “While some companies stop after a Type-1, we wanted to make sure our customers know we are committed to having a third-party ensure we do what we say we are going to do.”
In August 2019, Sign In Enterprise received the SOC 2 Type-2 attestation, setting a high standard for compliance and customer security.
“This means that our platform and our customers data is there when they need it and that only authorized humans have access,” said Tuba. “By choosing a VMS that takes security seriously, you can show that you take security seriously.”
